
As more and more teams are adopting the fully-managed database-as-a-service model to simplify database administration, we’ve experienced a surge of growth in our ScyllaDB Cloud user base. In response to the needs of this growing user base, we’re excited to announce a number of updates many customers have been waiting for: the ability to independently resize your clusters, a Terraform provider that makes it easier to control ScyllaDB Cloud as part of a larger infrastructure, SSO, new regions/instances, and more.
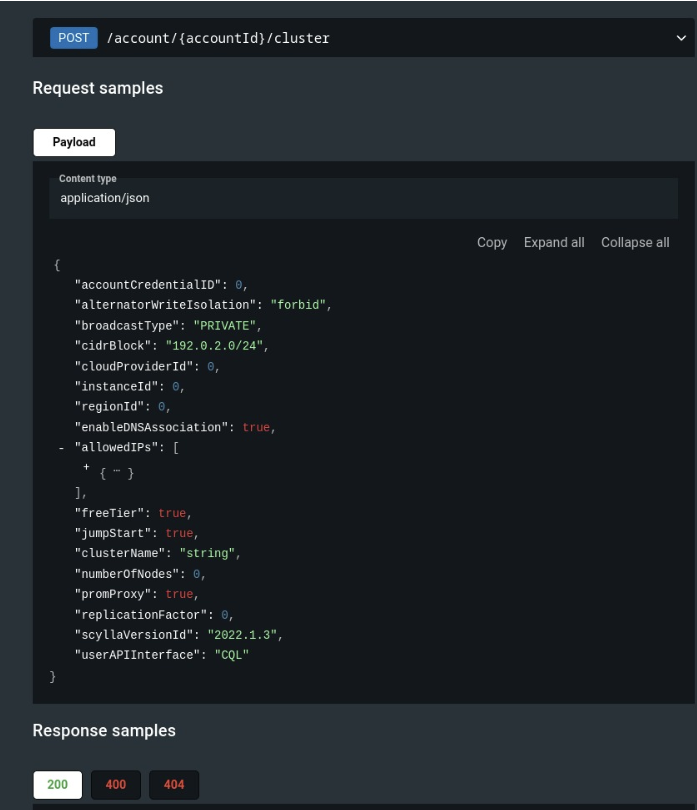
ScyllaDB Cloud Admin API
The ScyllaDB Cloud Admin API was extended to give users the ability to independently resize their clusters. This means you can now easily scale out by adding more nodes or scale in by choosing a different instance type, all without needing external assistance. The API exposes operations like:
- Manage clusters (AWS / GCP / AWS BYOA)
- Manage firewall rules
- Manage networking configuration (including VPC Peering)
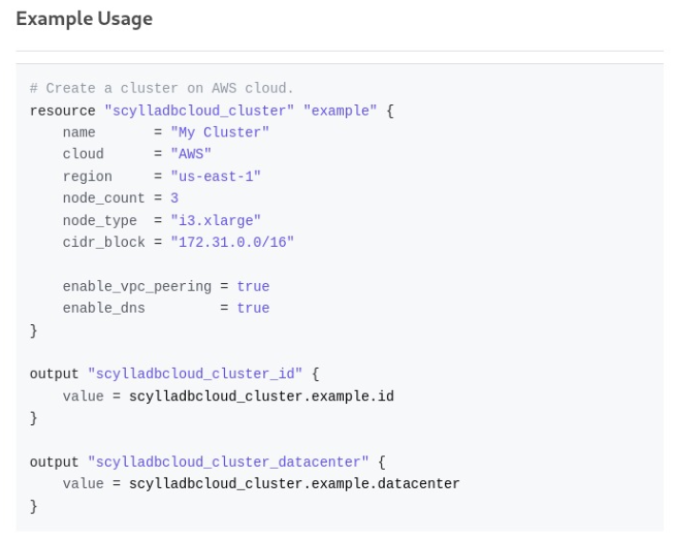
ScyllaDB Cloud Terraform Provider
Based on the Admin API (above), the Terraform provider makes it easier to control ScyllaDB Cloud as part of a larger infrastructure.
Full documentation is available in the Terraform Registry.
The project is open source under the following address on GitHub – scylladb/terraform-provider-scylladbcloud: Terraform provider for ScyllaDB Cloud. We welcome users to report feedback and we also welcome contributions – especially examples, new use cases and documentation!
Personal Tokens for the ScyllaDB Cloud API and Terraform Provider
You can now create Personal Tokens in your ScyllaDB Cloud accounts to access the ScyllaDB Cloud API and the ScyllaDB Cloud Terraform provider.
To add a Personal Token, navigate to Settings > Personal Tokens. From there, you’ll be able to generate Personal Tokens.
If you have access to multiple ScyllaDB Cloud accounts, ensure you create a new personal token in each of the relevant accounts.
This feature replaces legacy API keys. Legacy API Keys will be deprecated on January 1, 2024. Users who have an active legacy API key will receive an email with steps on how to generate a Personal Token in ScyllaDB Cloud. For more information, see our API docs.
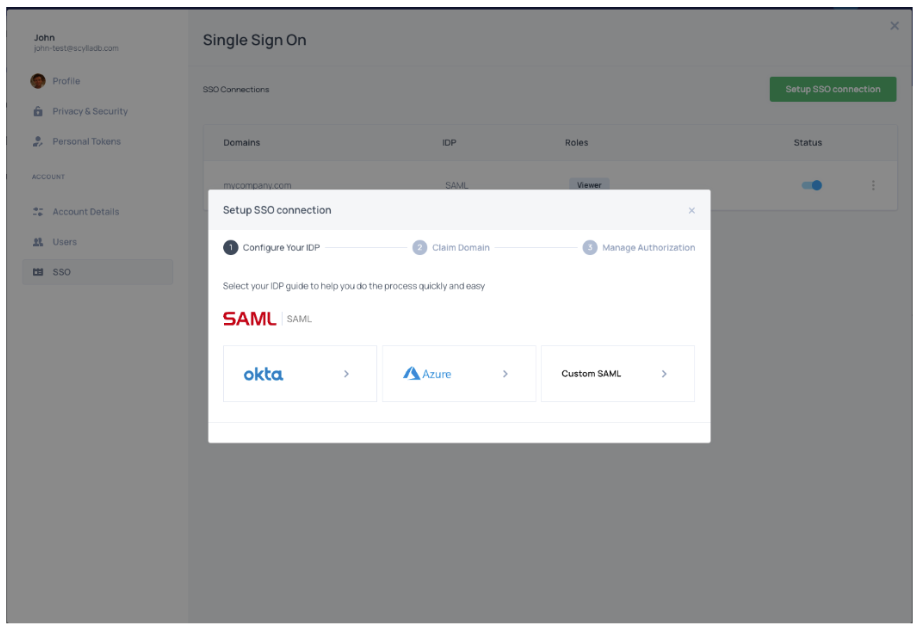
Single-Sign On
You can now securely authenticate with multiple applications using one set of credentials via SAML SSO. If SAML is enabled and configured in your organization, you can configure an SSO connection directly from ScyllaDB Cloud and allow other users to sign in to your ScyllaDB Cloud account using SAML SSO.
See the SSO documentation for details.
Encryption at Rest with BYOK
Encryption at rest protects your cluster data against unauthorized access. It renders stored data (at rest) unreadable unless a secret encryption key is provided. In ScyllaDB Cloud, your data is always encrypted on the storage level by a cloud provider, such as AWS. To add another layer of security, we recommend enabling encryption at rest at the database (DB) level.
With the 2023.1.x release (expected for November 2023), you can use an encryption key you created in your own Key Management Service (KMS) on AWS to safeguard data at rest at the database level.
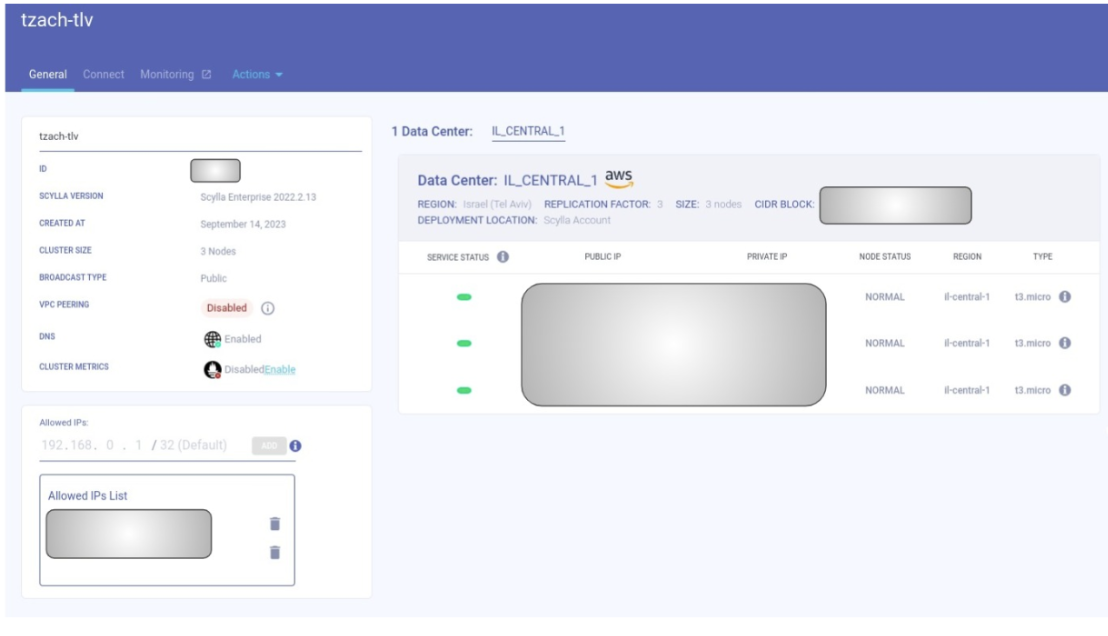
New Regions and Instances
We’ve launched in the AWS Israel region
AWS recently launched the AWS Israel Region, with three availability zones, and we’re one of their initial launch partners! ScyllaDB Cloud is now available in this region (and so are ScyllaDB Enterprise and ScyllaDB Open Source).
Google Cloud’s Delhi region is now supported
Our Google Cloud customers can now run ScyllaDB in the asia-south2 (Delhi) GCP region.
New AWS instances available
We’ve added support for i3en AWS instances in the ap-southeast-2 (Sydney) region. Additionally, we now support i4i and i3en AWS instances in the ap-south-1 (Mumbai) region.





